Malware families and ransomware campaigns adopt different strategies – phishing, information stealing, cryptomining, etc. – to succeed in your investees
Picus Labs and CLM, a Latin American value-added distributor focused on information security, data protection, cloud and infrastructure for data centers, value-added distributor of Picus, list the top five cyberthreats that victimized thousands of organizations in the last month. Are they:
Iranian government-sponsored APT (Advanced Persistent Threat) malicious actors have deployed a cryptominer and credential harvester on US federal networks.
The Hive ransomware, which affected more than 1,300 companies, caused $100 million in ransom payments.
Backdoor loader TONESHELL, whose attacks were perpetrated by the group Earth Preta, also known as Mustang Panda and Bronze President, use fake Google and DropBox accounts, with the use of APT.
New variant of the Koxic ransomware that, despite having appeared in Korea, has perpetrated attacks all over the world. Koxic reconfigures the system, disables real-time monitoring features, including behavioral ones, preventing detection by Windows Defender.
Aurora Malware, which initially emerged as a Malware-as-a-Service (MaaS) botnet with data theft and remote access capabilities. In September, cybersecurity researchers found that it had become an infostealer, and in November, from analysis of many active C2 servers, it was found that Aurora was the number one infostealer used by malicious actors.

Francisco Camargo
Whatever the scenario, says CLM CEO Francisco Camargo, in order to prevent these and other threats, it is essential to carry out simulations and test the companies' defenses. “It's worth mentioning that, according to a Picus Library report released this week, although most firewalls detect and block, for example, SQLi attacks quite easily. Recent research has shown that many vendors of web application firewalls (WAF) have failed to block SQLi attacks that exploit JSON for delivery. Picus Labs has added this new WAF bypass method for SQL injection to the Picus Threat Library.”
Detailed information on the five cyberthreats
For those who need more details about these five threats, it is worth checking out more details, including the tables, whose various cyberthreats related to these attacks were included by Picus in its library.
1. Agents of Iranian APTs who attacked FCEB (AA22-320A)
On November 16, 2022, CISA (Cibersecurity & Infrastructure Security Agency) and the FBI issued a joint statement regarding the attack campaign of these APT agents, who exploited the unpatched Log4Shell vulnerability to access a VMware Horizon server, which belongs to a organization of the Civilian Federal Executive Branch (FCEB) of the United States. On initial access, cybercriminals allowed specific directories to download malicious tools without being noticed by virus scans. Afterwards, they ran a PowerShell script to disable Windows Defender and downloaded malicious files and software (XMRig crypto miner) onto the target system, which was later leveraged to establish persistence and use the victim's computing power to mine cryptocurrency.
The attackers then move laterally from the compromised Horizon VM server to the VMware VDI-KMS host using a built-in Windows user account over an RDP connection. Later they ported some tools to the VID-KMS host (Mimikatz, PsExec, ngrok) for post-exploitation activities. Finally, they were able to gain full control over all assets associated with the domain, including the domain controller.
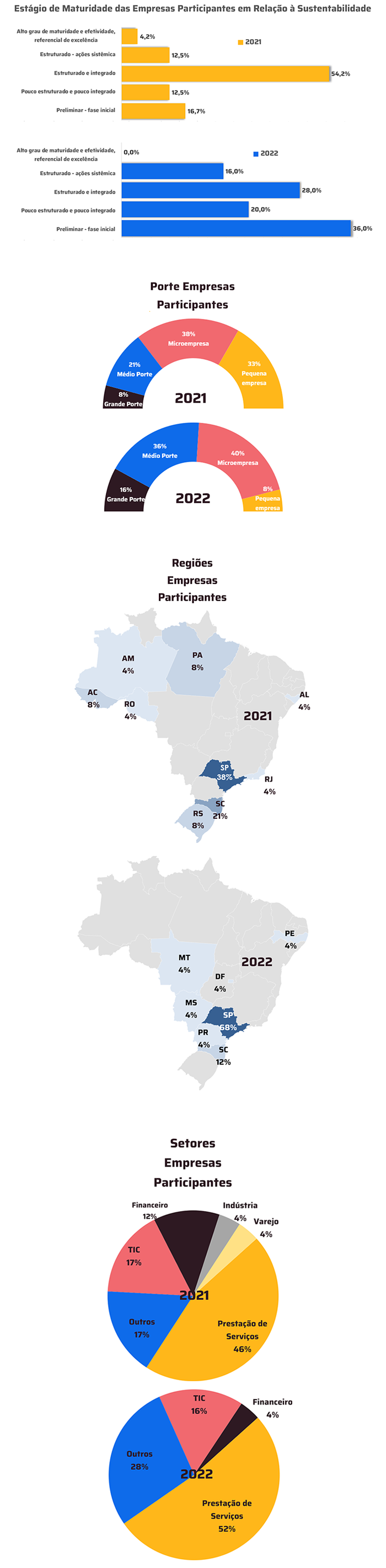
Picus Threat Library included the following for the Iranian APT:
2. Hive Ransomware (AA22-321A)
holders of hive ransomware use different initial access techniques. However, Picus Labs has observed that they send phishing emails with a malicious attachment designed to exploit known vulnerabilities in public-facing applications such as Windows Exchange Servers.
Once the foothold is gained, Hive agents download malicious binaries and an obfuscated Powershell script, which is part of the Cobalt Strike framework, from their C2 server. By compromising the local computer's most powerful internal user, NT Authority, attackers dump all NTLM hashes to leverage a Pass-the-Hash (PtH) attack.
Using stolen valid account credentials, criminals send RDP (Remote Desktop Protocol) connection requests to many internal assets to see which databases they have access to. It is suspected that this was done to check the expansion of their access and find out what sensitive information they can exfiltrate before encryption begins. Then, having a list of all domain objects, attackers run a batch script to ping all items in the list and record those that respond to a file. These files are further encrypted for greater impact.
“In fact, cyber espionage exploiting Google Drive for C2 infrastructure has been reported by other leading cybersecurity companies, such as Netskope”, mentions Camargo.
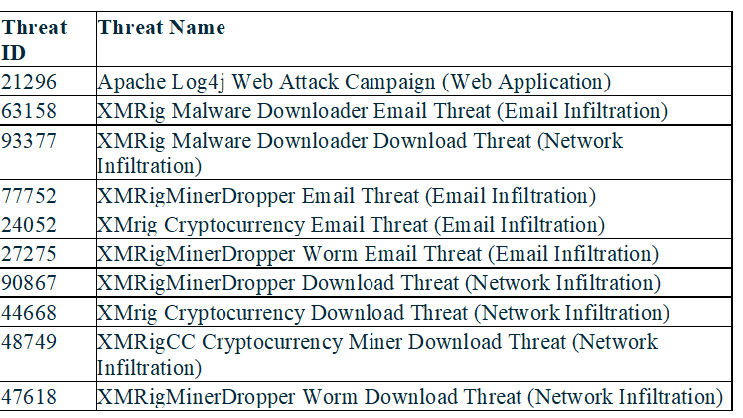
Picus Labs has added new attack simulations to the Picus Threat Library for new malware used by Hive agents.
3. TONESHELL backdoor loader, whose attacks were filed by the group, which uses APT, Earth Preta, also known as Mustang Panda and Bronze President. These crackers use fake Google and DropBox accounts, sending spearphishing with a malicious Google Drive or DropBox link attached to them to deploy the Hive malware.
“From March 2022, we begin to see new cyber-espionage activity,” says the Picus Labs report. According to security researchers, this attack campaign originates from an Advanced Persistent Threat (APT) agent. Analysis shows that the attachments contain malicious files (rar/zip/jar) such as images (.png), word documents (.doc) and legitimate executables (.exe), which have benign-looking names that trick victims into thinking they come from government sources. But in reality, they trigger the execution of the following malware families: TONEINS, TONESHELL and PUBLOAD.
Among these three malware, TONESHELL is the backdoor mainly used by Earth Preta in its targeted phishing campaigns. TONESHELL is loaded and decoded on the target system via the shellcode loader called Backdoor.Win32.TONESHELL. Further analysis shows that the TONESHELL payload code contains several functions with self-explanatory strings used for file upload, download and execution, lateral movement and intranet data exchange via OnePipeShell, unidirectional shell over a named pipe and TwoPipeShell functions.
Once the backdoor is installed and encrypted C2 communication is established, attackers exfiltrate sensitive information as part of their double extortion method.
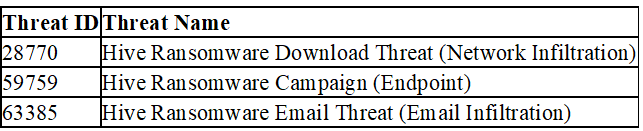
Picus Labs had already included threats for Mustang Panda. Now added to the Picus Threat Library the following threats for TONESHELL backdoor, TONEINS malware dropper and PUBLOAD malware downloader:
4. Koxic ransomware – new variant. Despite having originated in Korea, Koxic has perpetrated attacks around the world. It reconfigures the system, disables real-time monitoring features, including behavioral ones, preventing Windows Defender detection.
Upon execution, Koxic ransomware initiates a discovery phase to recover current system information. It then resets the RDP expiration to its maximum to maintain a longer remote desktop session and disables Windows Defender's behavior and real-time monitoring features to evade detection and prevent defense systems from sending email notifications. alert to SIEM systems.
HKLM\SOFTWARE\Policies\Microsoft\Windows NT\Terminal Services\MaxDisconnectionTime HKLM\SOFTWARE\Policies\Microsoft\Windows NT\Terminal Services\MaxIdleTime
HKLM\SOFTWARE\Policies\Microsoft\Windows Defender\DisableAntiSpyware
HKLM\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection\DisableRealtimeMonitoring HKLM\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection\DisableBehaviorMonitoring HKCU\Software\Policies\Microsoft\Windows\Explorer\DisableNotificationCenter
The ransomware continues its flow, deleting volume shadow copies and disabling database services such as MongoDB, SQLWriter, and MySQL. Then, the malware starts making a list of all targets that can be encrypted. As a parallel process, this is a threat that goes through this list, encrypting each item one by one. Encryption is performed using the AES algorithm in CBC mode, where the initialization value (IV) value and the symmetric key for the AES algorithm are encrypted by an asymmetric encryption algorithm, RSA.
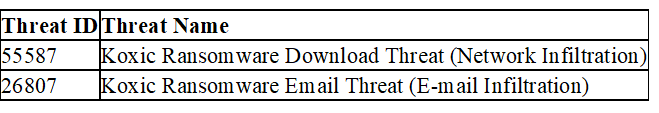
The Picus Threat Library includes the following threats for Koxic ransomware:
5. Aurora Malware initially emerged as a Malware-as-a-Service (MaaS) botnet with data theft and remote access capabilities. In September, cybersecurity researchers found that it had become an infostealer, and in November, from analysis of many active C2 servers, it was found that Aurora had become the number one infostealer used by malicious actors. “The data is exfiltrated in JSON format from the target system to an attacker-owned Aurora C2, which listens for incoming network traffic on ports 9865 and 8081 over TCP,” details the Picus Labs report, which had already observed different RATs (PoetRAT, FairFAX) used in Aurora malware campaign in 2021.
In April 2022, Aurora was first announced on Russian-speaking hacking forums and the Telegram channel as a Malware-as-a-Service (MaaS) botnet with data-stealing and remote access capabilities. As of August 2022, its activity has almost disappeared; being suspected that its developers stopped selling it and removed its code from underground repositories.
However, in September 2022, a new and large Aurora activity caught the attention of security researchers, revealing itself not as a botnet, but as an “infostealer”. It became so popular that many big drug teams suggested its use. By November 2022, an analysis of many active C2 servers showed that Aurora had become the number one infostealer used by hostile agents.
Aurora primarily uses the lxn/win library for system-related information, which depends on WMIC. The following wmic commands are executed on the infected host:
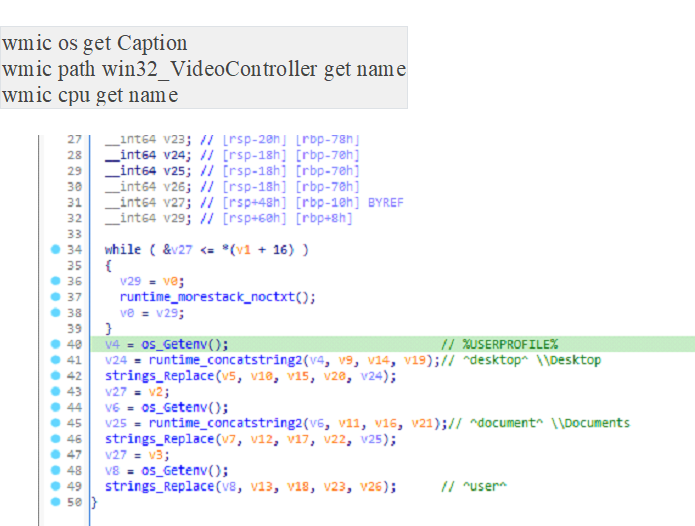
Data is exfiltrated in JSON format from the target system to an attacker-owned Aurora C2, which listens for incoming network traffic on ports 9865 and 8081 over TCP.
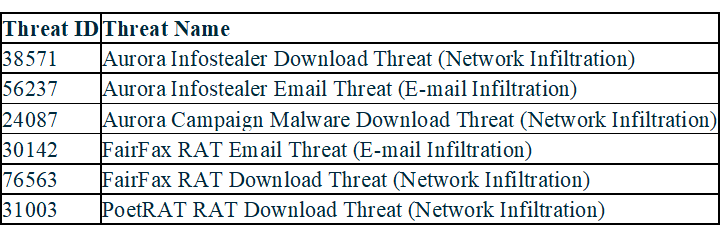
The Picus Threat Library now includes the following threats for the Aurora infostealer malware: