Managed Services Provider (MSP) Solo Network Warns Cloud Adoption Requires Alignment with Security Best Practices

By 2025, 51% of IT spending in the application, infrastructure software, outsourced services and system infrastructure markets will have migrated from traditional solutions to the public cloud. And nearly two-thirds (65.9%) of application spending will go to cloud technologies in 2025, up from 57.7% in 2022, according to a survey by Gartner???????? The IDC study “Predictions Brazil 2022”, reveals that more than 95% of organizations that already use the cloud will preserve or expand the capacity of these environments.
“In 2022, migration to the cloud has been intense. And for this movement to be successful, companies need to align themselves with the best security practices available in the market, otherwise the continuity of the company's business can be compromised, as well as the theft, and consequently, the leakage of data. information", explains Eduardo Martins, Director of Services at Solo Network.
Migrating to the Cloud: What to Watch Out For
Regardless of whether you opt for a public cloud (with reduced costs), private cloud (customized to the customer's needs) or hybrid cloud (a mix of both), when we talk about security, the most important thing is to pay attention to where your company's sensitive data will stay hosted. On which company's server? which country? Will my team have training and immediate response?
local legislation
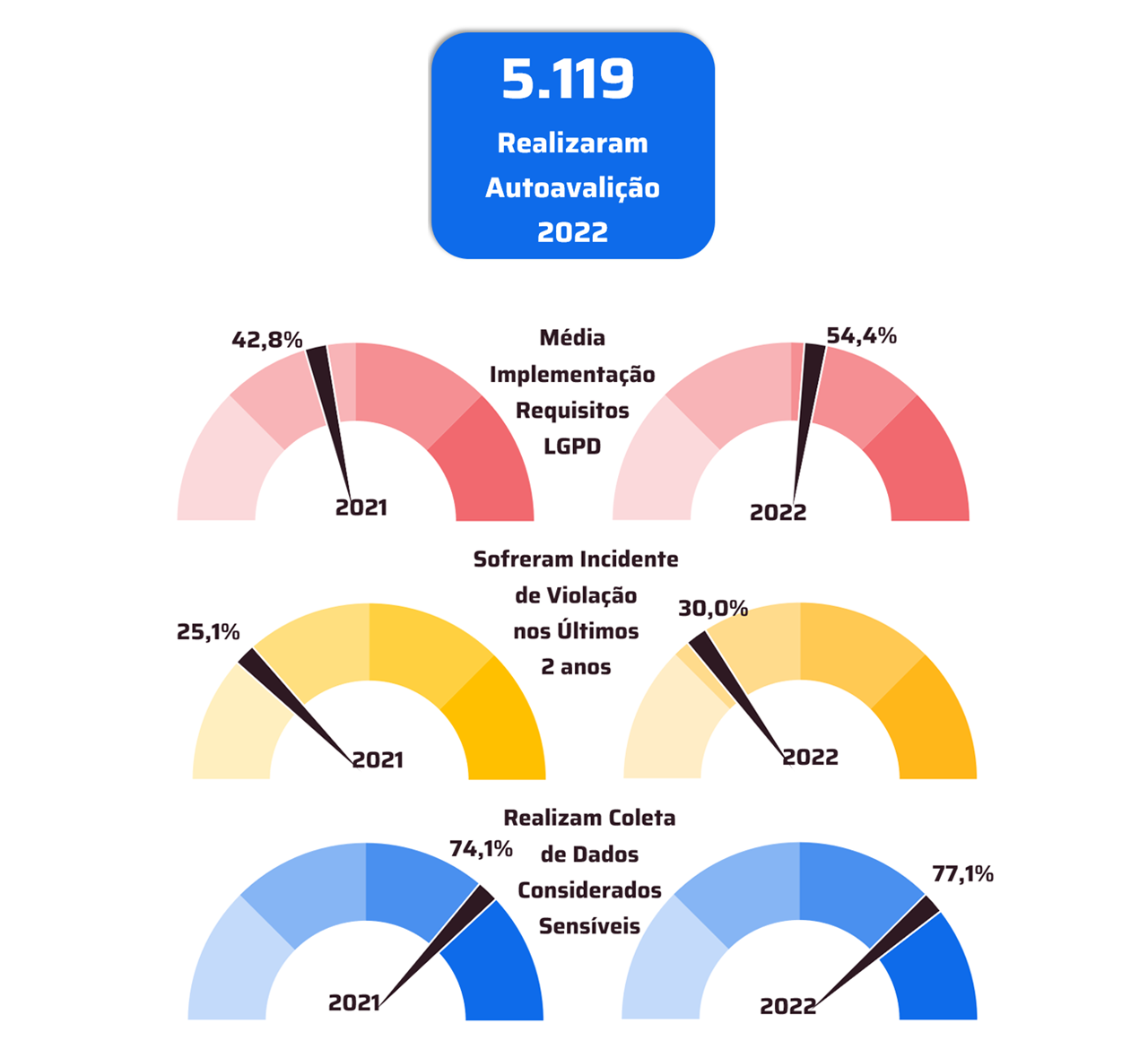
When data from a large Brazilian company is stored outside the country, in addition to the need to comply with the LGPD (General Data Protection Law), it is essential to comply with the law of the country in question. And this directly influences cloud security. In the US, for example, there is specific legislation for handling data in the cloud, which even allows your government to have access to everything that is hosted there, if necessary for national security. Other countries have different conducts in this regard. We always need to understand if the company's compliance is in accordance with local legislation and if this legislation will help protect the information of the company and its customers and users.
Support
In addition, there is the issue of 24/7 support. Currently, many cloud provider companies already have local support in the required language and time zone. However, it is important to look at this point. If a company is Brazilian, but the data is hosted in China, for example, if there is any damage to the cloud during business hours in Brazil, the company needs to know in advance if there is local Chinese support that respects the time zone or has , at least one time zone smaller than 11 or 12 hours. In this way, one avoids delay of response that can cost the company's reputation and information in the event of an attack.
conscientious collaborator
When having data in the cloud, it is essential that the company's team is well trained to ensure that information is saved in the correct place. Generally, especially in private clouds, there are specific places to store sensitive data. And this should be addressed during training of your employees with the supplier team of the chosen solutions.
Security levels per employee
In addition, still on the subject of employees, it is necessary to give access to information to those who need this information. After all, it makes no sense for a company's marketing professional, for example, to have full access to factory floor data. Unless this is going to be used strategically by your area, in which case this employee will have temporary authorization for such access. This ensures that no confidential information falls into the wrong hands or is even shared, with or without malicious intent, outside the company.
High Availability
This question is fundamental when hiring a cloud. It's what keeps the company's business going even if the main data center fails. Microsoft Azure, for example, offers availability zones that allow you to achieve data resiliency through backups, for example. Thus, if your company suffers a ransomware attack or DDoS (Denial of Service Attack) your team will be able to count on high availability to provide holistic resilience to the company's information while the problem is solved by the security team. disaster recovery.
“Information security is not done by one aspect or another, but by a wide range of functionalities that can help prevent or mitigate attacks by cybercriminals. I believe that the moment of choosing efficient cloud computing solutions that are suitable for your business model is one of the fundamental points. This aspect should be closely linked to the training and qualification of internal teams in handling information and responding to incidents. With this, the company can become much safer”, concludes the executive.