The highly targeted trojan that continues to claim victims in large companies and institutions
The researchers of Trend Micro, a world leader in cybersecurity solutions, analyzed the behavior of the RansomEXX, family of ransomware that gained notoriety in 2020, after being used in attacks against large institutions and public and private companies, and that last year brought down the operations of one of the largest Brazilian retail chains.
Operating in the Ransomware-as-a-Service (RaaS) model, the malware attacks both Windows-controlled and Linux-based machines, thus making it possible to compromise the infrastructure. Among the group's techniques and tactics are the use of the target organization's name in the binary code, and the victims' names both in the email address used to carry out the blackmail and in the extension of encrypted files.
O RansomEXX is linked to the group of cybercriminals Gold Dupont, whose motivation is financial and has other known malware in its arsenal such as Cobalt Strike, Metasploit and Vatet Loader. The combination of memory-based techniques, legitimate Windows tools, and post-intrusion contribute greatly to the success of intrusions.
According to a Trend Micro survey, Brazil is the third country in the world to receive more attacks from RansomEXX, right behind the United States and France, which occupy, respectively, the first and second places in the ranking, which also has Taiwan and Germany among the main targets.
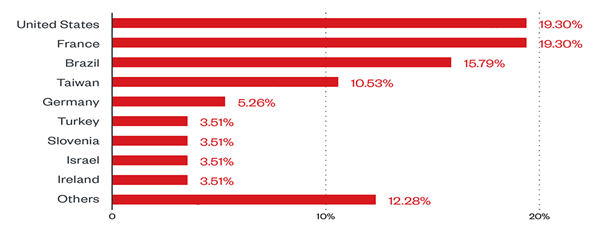
Countries with the highest number of RansomEXX attack attempts (March 31, 2021 to March 31, 2022). Source: Trend Micro™ Smart Protection Network™
Based on detections by the Trend Micro™ Smart Protection Network™ tool, the most affected sectors by the group are industry, with the most attack attempts, followed by far by education, finance and technology.
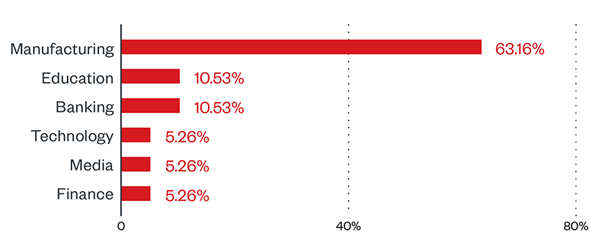
Sectors with the highest number of attack attempts (March 31, 2021 to March 31, 2022). Source: Trend Micro™ Smart Protection Network™
RansomEXX often uses a malspam to infiltrate machines, providing various tools and malware before finally deploying ransomware. They use, for example, IcedID TrickBot, Cobalt Strike and PyXie RAT, known for other campaigns. The strategy facilitates system contamination and the ability to steal data and obtain information from the target machine.
“To prevent these attacks, it is critical that organizations and businesses have a security solution that contains the capabilities to establish a solid defense against ransomware. One of the effective forms of protection is the adoption of a multi-layered platform to detect suspicious behavior, which helps to block dubious processes and tools from the beginning, before ransomware can cause irreversible damage to the system”, highlights César Cândido, director of Trend Micro Brasil.